Debugging TLS problems: Difference between revisions
Jump to navigation
Jump to search
No edit summary |
No edit summary |
||
| (One intermediate revision by the same user not shown) | |||
| Line 22: | Line 22: | ||
And then process in wireshark using the ssl.handshake filter. Look for the Secure Socket Layer section | And then process in wireshark using the ssl.handshake filter. Look for the Secure Socket Layer section | ||
[[File:Ssl.handshake filter.png|400]] | |||
Enable LEGACY support | Enable LEGACY support | ||
Latest revision as of 07:27, 19 April 2026
There is a problem with CentOS 9 and TLS with Asterisk. These tools may help to identify the issue
List all the ciphers available
openssl ciphers -v
Check the ciphers available on a SSL server
openssl s_client -connect pbx.mirtapbx.com:5061 -cipher ALL
or using nmap
nmap --script ssl-enum-ciphers -p 5061 pbx.mirtapbx.com
Check the protocols available on SSL server
testssl.sh pbx.mirtapbx.com:5081
To check for the ciphers available on a client, dump the packets with tshark
tshark -i eth0 -w /var/www/html/tls.pcap -s 1500 -f 'host 176.206.10.252 and port 5061'
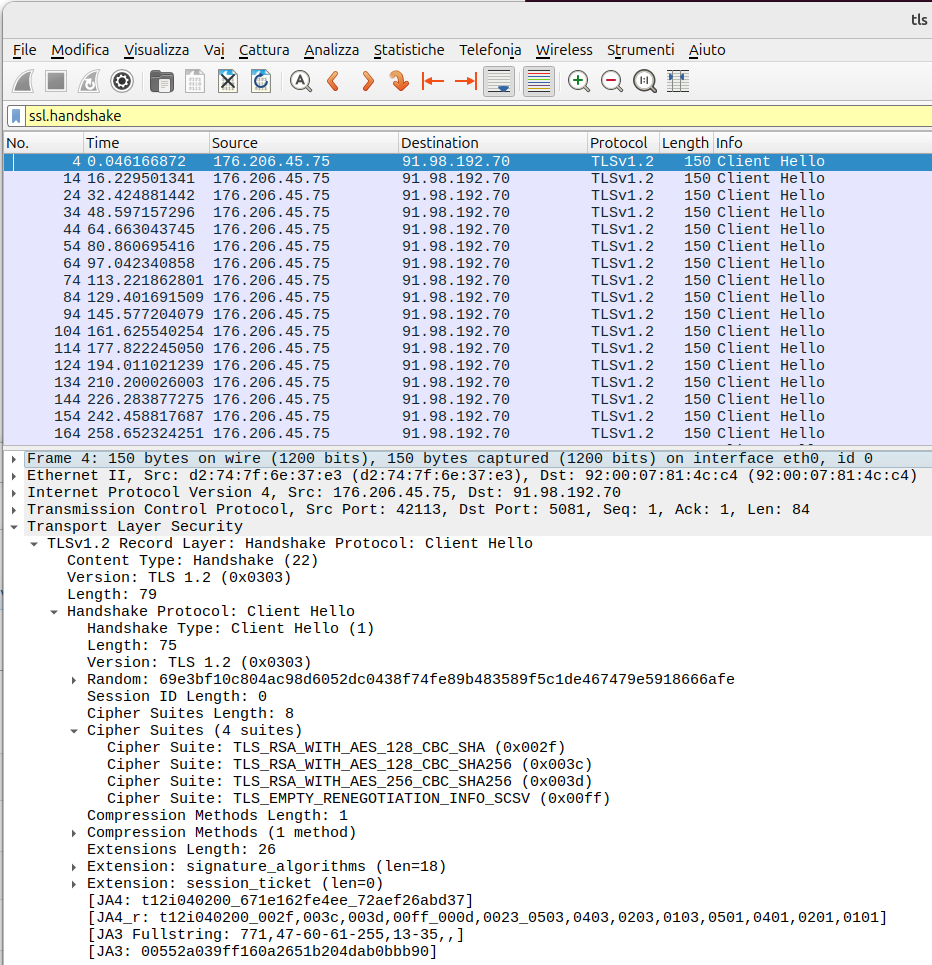
And then process in wireshark using the ssl.handshake filter. Look for the Secure Socket Layer section
Enable LEGACY support
update-crypto-policies --set LEGACY
Check support level
update-crypto-policies --show
In pjsip.conf now you can use
method=tlsv1_2 cipher=DEFAULT,@SECLEVEL=1